Installing prerequisite
|
1 |
sudo apt-get install git-gui gitk meld kdiff3 |
Configuring Git Environment
First config your environment and set a proper merge/ diff tool. The settings in Linux are under/home/<username>/.gitconfig. If you don’t know where this file is located in your OS You can easily edit this file by:
|
1 |
git config --global -e |
All Git settings can be set or viewed via terminal, i.e:
|
1 |
git config --list --show-origin |
If the URI of your repository is file-based, you can enable cloning by:
|
1 |
git config --global protocol.file.allow always |
To view all settings
|
1 |
git config --list --show-origin |
Current settings of mergetool:
|
1 |
git config --global merge.tool |
Set the merge tool
|
1 |
git config --global merge.tool vimdiff |
All available options for setting a merge tools can be listed by:
|
1 |
git mergetool --tool-help |
here we config it for meld, kdiff3 and vim.
Kdiff3
Add the following to your .gitconfig file
|
1 2 3 4 5 6 7 8 9 10 11 12 13 14 |
[diff] tool = kdiff3 guitool = kdiff3 [difftool] prompt = false [difftool "kdiff3"] path = /usr/bin/kdiff3 trustExitCode = false [merge] tool = kdiff3 [mergetool "kdiff3"] path = /usr/bin/kdiff3 keepBackup = false trustExitCode = false |
For Windows users:
|
1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 23 |
[core] editor = \"C:/Program Files (x86)/notepad++/notepad++.exe\" -multiInst -nosession autocrlf = true [pull] rebase = false [fetch] prune = false [rebase] autoStash = false [diff] guitool = kdiff3 [difftool "kdiff3"] path = C:/Program Files/KDiff3/kdiff3.exe cmd = \"C:/Program Files/KDiff3/kdiff3.exe\" \"$LOCAL\" \"$REMOTE\" [merge] tool = kdiff3 guitool = kdiff3 [mergetool "kdiff3"] path = C:/Program Files/KDiff3/kdiff3.exe cmd = \"C:/Program Files/KDiff3/kdiff3.exe\" \"$BASE\" \"$LOCAL\" \"$REMOTE\" -o \"$MERGED\" [user] name = <your-username> email =<your-email> |
Meld
|
1 2 3 4 5 6 7 8 9 10 11 12 13 14 |
[diff] tool = meld [difftool "meld"] path = /usr/bin/meld trustExitCode = false [difftool] prompt = false [merge] tool = meld [mergetool "meld"] path = /usr/bin/meld trustExitCode = false [mergetool] keepBackup = false |
For Windows users:
|
1 2 3 4 5 6 7 8 9 10 |
[difftool "meld"] path = C:/Program Files (x86)/Meld/Meld.exe cmd = \"C:/Program Files (x86)/Meld/Meld.exe\" \"$LOCAL\" \"$REMOTE\" [diff] guitool = meld [mergetool "meld"] path = C:/Program Files (x86)/Meld/Meld.exe cmd = \"C:/Program Files (x86)/Meld/Meld.exe\" \"$BASE\" \"$LOCAL\" \"$REMOTE\" -o \"$MERGED\" |
Vim
|
1 2 3 4 5 6 7 8 9 10 11 |
[merge] tool = vimdiff conflictstyle = diff3 [mergetool] prompt = false [diff] tool = vimdiff [difftool] prompt = false [alias] d = difftool |
Username, Email, and editor
|
1 2 3 4 5 |
[core] editor = /usr/bin/gedit [user] email = behnam.asadi@gmail.com name = behnam.asadi |
Adding Alias
[alias]
|
1 |
graph = log --all --decorate --graph --oneline |
or add it via the terminal:
|
1 |
git config --global alias.graph 'log --all --decorate --graph --oneline' |
Multiple GitHub accounts with SSH keys
First, create your keys:
|
1 |
ssh-keygen -t [dsa | ecdsa | ecdsa-sk | ed25519 | ed25519-sk | rsa] -C "comment-your-email" -f <filename> |
and upload your public key, located at
/home/<username>/.ssh/id_rsa.pub
into your GitHub account
If you have multiple accounts, you can create the following config file and save it under /home/<username>/.ssh/config directory. The Host value could be anything, but you should be persistent: in our case, these values are:
- github.com-first-account
- github.com-second-account
The first-account and second-account are your real GitHub user account ID
The content of the config file:
|
1 2 3 4 5 6 7 8 9 10 11 12 13 |
#your-first-account, Host github.com-first-account HostName github.com AddKeysToAgent yes User git IdentityFile ~/.ssh/id_rsa_your-first-account.pub #your-second-account Host github.com-second-account HostName github.com AddKeysToAgent yes User git IdentityFile ~/.ssh/id_rsa_your-second-account.pub |
If you copy your key from a machine to your .ssh directory, the permissions are too open and you will get
|
1 2 |
WARNING: UNPROTECTED PRIVATE KEY FILE! Permissions 0755 for '/home/etc.ssh/id_rsa' are too open. |
So you need to:
|
1 2 |
chmod 600 ~/.ssh/id_rsa; chmod 600 ~/.ssh/id_rsa.pub |
Also, /home/<username>/.ssh/ the directory itself must be writable only by you:
|
1 |
chmod 700 ~/.ssh |
Add the keys to ssh-agent, first:
|
1 |
eval "$(ssh-agent)" |
SSH needs two things in order to use ssh-agent: an ssh-agent instance running in the background, and an environment variable set that tells SSH which socket it should use to connect to the agent (SSH_AUTH_SOCK IIRC). If you just run ssh-agent then the agent will start, but SSH will have no idea where to find it [1]
Then add the key to ssh-agent:
|
1 2 |
ssh-add ~/.ssh/id_rsa_firstkey ssh-add ~/.ssh/id_rsa_otherkey |
and list them:
|
1 |
ssh-add -l |
confirm the connection:
|
1 2 3 4 |
ssh -T github.com-first-account ssh git@github.com-first-account ssh -T github.com-second-account ssh git@github.com-second-account |
or directly:
|
1 2 |
ssh -Ti ~/.ssh/id_rsa_first-account git@github.com ssh -Ti ~/.ssh/id_rsa_second-account git@github.com |
you can debug everything:
|
1 |
ssh -vvvT git@github.com |
passphrases for SSH keys
if someone gains access to your machine, the attacker can gain access to every system that uses that key. You can add a passphrase to your SSH key to encrypt it. To avoid entering the passphrase every time you connect, you can securely save your passphrase in the SSH agent.
Change the passphrase for an existing private key without regenerating the keypair:
|
1 |
ssh-keygen -p -f ~/.ssh/id_rsa |
Change the passphrase comment:
|
1 |
ssh-keygen -c -C "behnam.asadi@gmail.com" -f ~/.ssh/id_rsa_behnamasadi |
now, while cloning repositories instead of :
|
1 |
git clone git@github.com:personal_account_name/repo_name.git |
you use:
|
1 |
git clone git@github.com-first-account:first-account/repo_name.git |
and
|
1 |
git clone git@github.com-second:second-account/repo_name.git |
For existing repositories:
|
1 |
git remote set-url origin git@github.com-first-account:first-account/repo_name.git |
and
|
1 |
git remote set-url origin git@github.com-second-account:second-account/repo_name.git |
Another solution is to have only one active SSH key in the ssh-agent at a time:
|
1 2 3 4 5 |
ssh-add -D eval "$(ssh-agent -s)" kill -9 <pid> eval "$(ssh-agent -s)" sh-add ~/.ssh/id_rsa-first-account |
Push into GitHub without a password using ssh-key
You have to change your remote type from http to git:
|
1 |
git remote set-url origin git@github.com:<username>/<repository_name>.git |
For example, if your repository is:
|
1 |
https://github.com/behnamasadi/data_structure_algorithm |
Then you have to run the following:
|
1 |
git remote set-url origin git@github.com:behnamasadi/data_structure_algorithm.git |
How to show the current branch in the Bash prompt
Edit ~/.bashrc and find the following lines and uncomment them
|
1 2 3 4 5 |
if [ "$color_prompt" = yes ]; then PS1='${debian_chroot:+($debian_chroot)}\[\033[01;32m\]\u@\h\[\033[00m\]:\[\033[01;34m\]\w\[\033[00m\]\$ ' else PS1='${debian_chroot:+($debian_chroot)}\u@\h:\w\$ ' fi |
and replace them with
|
1 2 3 4 5 6 7 8 |
parse_git_branch() { git branch 2> /dev/null | sed -e '/^[^*]/d' -e 's/* \(.*\)/(\1)/' } if [ "$color_prompt" = yes ]; then PS1='${debian_chroot:+($debian_chroot)}\[\033[01;32m\]\u@\h\[\033[00m\]:\[\033[01;34m\]\w\[\033[01;31m\] $(parse_git_branch)\[\033[00m\]\$ ' else PS1='${debian_chroot:+($debian_chroot)}\u@\h:\w$(parse_git_branch)\$ ' fi |
Disabling Unix file permissions problem:
If you get the following message during a merge:
|
1 2 |
old mode 100755 new mode 100644 |
You have to disable the file mode. This usually happens when the repo is cloned between Windows and Linux/Unix machines.
|
1 |
git config --global core.filemode false |
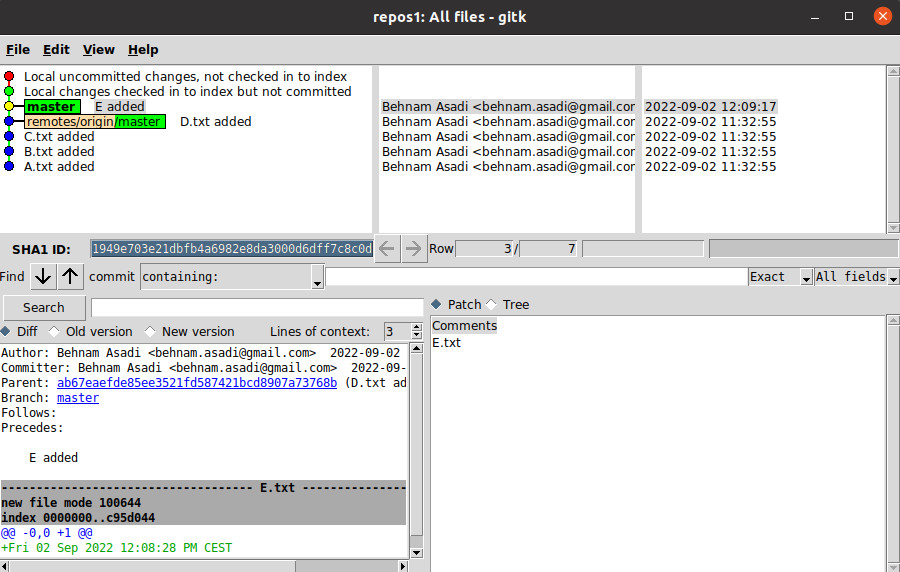
Colors in Gitk
Yellow: Commit with the yellow circle is the HEAD. Gitk jumps to this commit once it got opened.
Red: Commit with a red circle is your uncommitted changes.
Blue: All other commits are shown in the blue circle.
Green: Local branches names are shown in green,
Orange, and green: remote branch names are shown in a combination of orange and green, with the orange section being the remote name and the green section being the branch name.
Ignore list
you can use .ignore and .git/info/exclude
gitattributes
you can use .gitattributes and .git/info/attributes
Refs: [1]
How to get the root of Git repository
|
1 |
git rev-parse --show-toplevel |
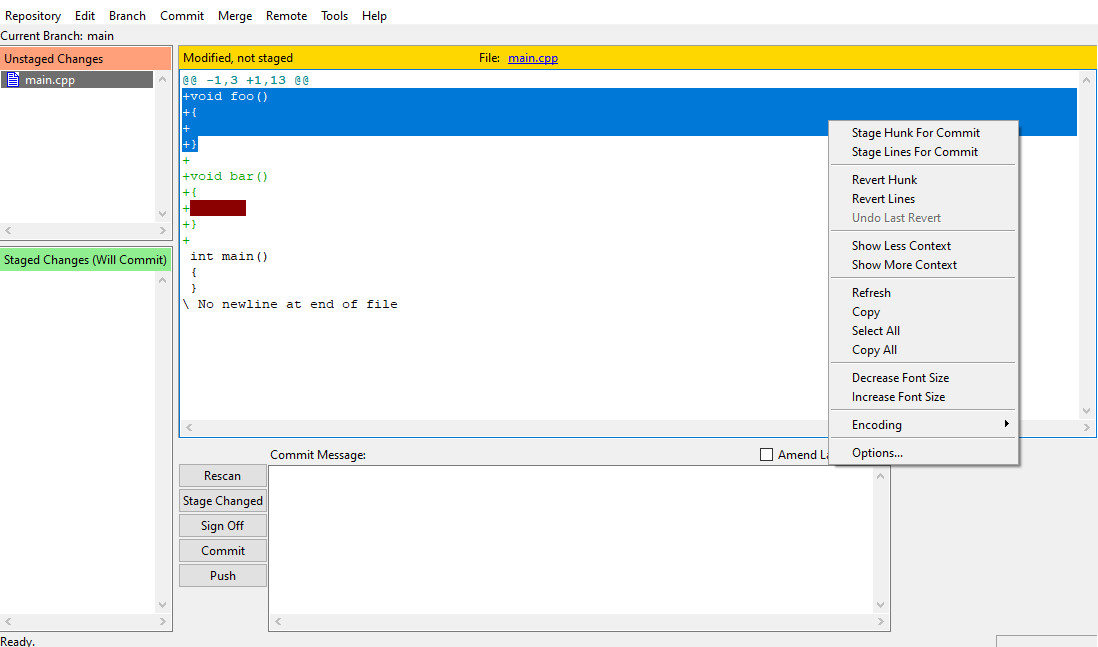
How to commit part of a file
You can use:
|
1 |
git add --interactive |
or
|
1 |
git add -p <<em>file</em>> |
and then
|
1 |
git commit |
not
|
1 |
git commit -a |
If you are using git-gui, you can mark chunks that you want to have included in the commit by right-clicking them and selecting: “Stage Lines For Commit”
Refs: [1]
Long filename problem in Git for Windows
|
1 |
git config --system core.longpaths true |
Refs: [1]